Configure Start Policies for Windows Devices Using Intune
In this post, I will go through the settings available to configure Windows Start using Intune.
There are 41 settings can be configured in the Start category and will list the most important settings and how to configure using existing Policy CSP.
Policy configuration service provider enables the enterprise to configure polices on Windows devices. Also, I will show the end user experience for the configured settings on Windows devices. We can configure the settings using Settings catalog and search the catalog you want to configure and deploy the policy to devices.
Start Policies in Intune:
The following start policies are available in Intune and we can use the below settings and deploy to Windows devices.
The system restart is required to take effect. I will explain a few start policies on how to configure and deploy to the devices and you can use the same process to deploy other start policies.
- AllowPinnedFolderDocuments
- AllowPinnedFolderDownloads
- AllowPinnedFolderFileExplorer
- AllowPinnedFolderHomeGroup
- AllowPinnedFolderMusic
- AllowPinnedFolderNetwork
- AllowPinnedFolderPersonalFolder
- AllowPinnedFolderPictures
- AllowPinnedFolderSettings
- AllowPinnedFolderVideos
- ConfigureStartPins
- DisableContextMenus
- DisableControlCenter
- DisableEditingQuickSettings
- ForceStartSize
- HideAppList
- HideChangeAccountSettings
- HideFrequentlyUsedApps
- HideHibernate
- HideLock
- HidePeopleBar
- HidePowerButton
- HideRecentJumplists
- HideRecentlyAddedApps
- HideRecommendedSection
- HideRestart
- HideShutDown
- HideSignOut
- HideSleep
- HideSwitchAccount
- HideTaskViewButton
- HideUserTile
- ImportEdgeAssets
- NoPinningToTaskbar
- ShowOrHideMostUsedApps
- SimplifyQuickSettings
- StartLayout
- Allow Pinned Folder Documents:
This setting controls the visibility of the document’s shortcut on the start menu and the below options can be configured.
- The shortcut is hidden and disables the setting in the Settings app.
- The shortcut is visible and disables the setting in the Settings app.
- There’s no enforced configuration, and the setting can be changed by the user.
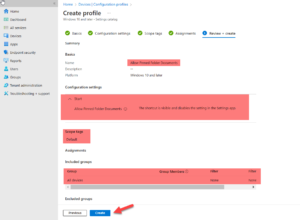
To configure the settings, log in to the Endpoint configuration manager portal and go to Devices -> Configuration Profiles. Click Create Profile.

Create configuration profile
Choose the platform to which you want to apply the profile and select Profile type “Settings catalog or Template.
In this post, I am going to apply the profile to Windows 10 and later Operation systems and settings catalog and Click Create to process further.

Choose platform and profile type
On the Basics page, specify the name & description and I have specified the profile name as “Allow Pinned Folder Documents” and click Next.

Specify the profile name
On the Configuration settings page, search the “start” category and select the “Allow Pinned Folder Documents” setting name. Once the setting is added to the page, the following three options are available.
Select “The shortcut is visible and disables the setting in the settings app” and click Next.
- The Shortcut is hidden and disables the setting in the settings app.
- The Shortcut is visible and disables the setting in the settings app.
- There is no enforced configuration, and the setting can be changed by the user.

Configure allow pinned documents setting
On Scope tags page, assign configured custom scope tag or select Default scope tag and Click Next.

Specify the scope tag
On the Assignments page, deploy the profile to all users or devices group and if you want to deploy the profile to specific devices, you can create a specific group and apply the profile. There is an option to exclude the groups if required. Click Next to continue.

Assign the device group to deploy the profile
On the Review + Create page, review the configured settings and once everything is fine, Click Create.
Review configured settings
The profile is created and it will list under Device | Configuration profiles. Click the profile to view the assignment status.

The profile is created
On the assignment status page, it will show the status of the targeted policy for the devices. I have deployed the policy to the device and it is applied successfully.

Policy assignment status
Result:
Before apply the policy: Document icon is not visible & documents option is not enabled in the settings app.

Before applying the policy
After apply the policy: Document icon is visible and it’s enabled in the settings app.

After applying the policy
- Hide Intune Change Account Settings
This setting allows the admins to configure start by hiding Change Account Settings. Enable the policy to apply the setting.
It is applicable to the following operating systems: –
Pro edition (Windows 10, Windows 11), Windows SE edition (Windows 11), Business edition (Windows 10, Windows 11), Enterprise edition (Windows 10, Windows 11), Education edition (Windows 10, Windows 11).
Please select Hide Change Account settings under the start category under the configuration settings page and enable the setting.
Configure the Scope tag, and assignment page as like above setting and click Create to deploy the policy to the machines.

Hide change account configuration setting
Result:
Before applying the policy: Change Account Settings appears in the start.

Before applying the policy
After applying the policy: Change Account Settings is not available in Start. To enforce the policy on the machines, Open the company portal and run the sync and wait for few minutes to apply the setting

After applying the policy
- Hide Restart in Intune
This setting allows the administrator to configure start by hiding “Restart” and “Update and restart” from the power button.
After applying the policy, Go to the Start -> Power button, and “Restart” and “Update and Restart” will not be available. It is applicable to the following operating systems: –
Pro edition (Windows 10, Windows 11), Windows SE edition (Windows 11), Business edition (Windows 10, Windows 11), Enterprise edition (Windows 10, Windows 11), Education edition (Windows 10, Windows 11).
The setting can be deployed only to devices and not to users. You can choose the Hide restart setting under the start category and enable it.

Hide Restart configuration setting
Result:
Before applying the policy: Restart option appears in the power button.

Before applying the policy
After applying the policy: There is no restart option now and you can also monitor the policy deployment status to the devices from portal and troubleshoot if there is any failure.

After applying the policy
- Hide The Shutdown
The administrator can configure the start to Hide “Shutdown” and “Update and Shutdown” from appearing in the power button and the options will not show after applying the policy.
We can apply the policy to the devices only and the status of Hide Shutdown policy available in Intune portal.

Hide Shutdown configuration setting
Result:
Before applying the policy: There are Disconnect, sign out and shut down appears in power button in the devices.

Before applying the policy
After applying the policy: Shutdown option is not available and only Disconnect, Sign out options sowing in power button.

After applying the policy
- Start Layout in Intune
This setting allows the administrator to override the default start layout and prevent the users to change it.
We can apply to devices and users as well. If you want users to view customized start layout, please use the Export-StartLayout PowerShell cmdlet in PowerShell to export into XML file.
To export the Start Layout to a .xml file:
- Open PowerShell as an administrator on the device and run Export-StartLayout using -UseDesktopApplicationID switch. For example:
Export-StartLayout -UseDesktopApplicationID -Path layout.xml

Poweshell commnd to export StartLayout
- Modify the exported xml file as per your requirements and apply to the devices using any deployment solutions.

StartLayout XML file
Wrapping it Up:
In conclusion, effectively configuring start policies for Windows devices using Intune is crucial for seamless device management in your enterprise.
With WME’s Intune services, you can confidently deploy and manage various start policies, tailoring the user experience to meet your organization’s needs.
Whether it’s controlling pinned folders, hiding specific settings, or customizing the start layout, WME’s Intune services provide comprehensive solutions to ensure a smooth and efficient device management process. Empower your organization with WME’s expertise and Intune services for a streamlined Windows device management experience.
Contact us by clicking here:






