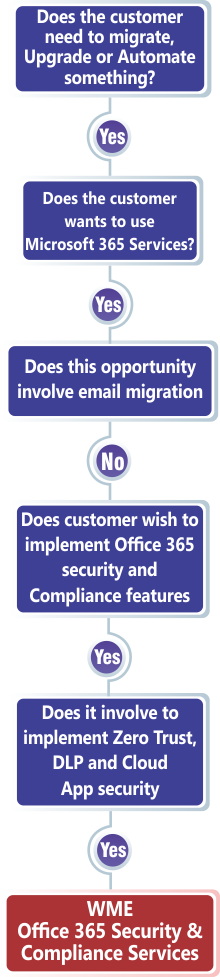
O365/ M365 Security & Compliance Services

Security Services for O365 / M365 & IaaS
WME’s Security & Compliance capabilities are second-to-none. By outsourcing your Office 365, Microsoft 365 & Microsoft Infrastructure-as-a-Service (IaaS) data protection to us, you can be sure that your data is safe, and consolidated by the excellence of a Microsoft Gold Partner company. Our security offerings not only meet global service standards but also keep adapting to the ever-changing professional landscape.

O365/M365 Migrations & IaaS Security Compliance & Risk Mitigation
WME offers dependable expertise to design & support your deployment solution, streamline Office 365 / Microsoft 365 security perfection, put your apps to work, and mitigate Shadow IT risks.
Safe & Secure Active Directory
We protect AD & ADFS by using all the expansive capabilities of MS Defender for Identity. Defender is certainly not an “end all be all” solution, but we make it so. We implement the layered security approach in the best possible way to keep your endpoints, emails, data, and applications secure. To ensure digital security for enterprises, usually, there’s a lot to be done about the architecture, and sensor requirements, taking proactive actions and doing so many other tasks, that we navigate skillfully without any compromises.
We eliminate all kinds of insider threats across your environment, no matter how complex it is. We offer complete visibility and control across all O365/M365 and Microsoft Infrastructure as a Service (IaaS) users, events, and users. We make comprehensive threat detection scans and design alerting protocols via continuous monitoring and automated coordination via the implementation of secure workflows to stop the leakage or overexposure of sensitive data.
Insider Risk Management
Data Loss Prevention
Organizations today hold sensitive information such as financial data, proprietary & trade secrets, credit card numbers, customer & employee data, and whatnot. We dive deep into your data landscape including SharePoint, and OneDrive. Using MIP capabilities like sensitive information types and trainable classifiers, we discover critical data across your environment. Then, we plan to protect your data using double key encryption, O365/M365 Message Encryption (OME), and many other capabilities.
Inquire Away! We've Got You Covered!
This is Protection beyond Office 365 / Microsoft 365 emails. WME’s protection offerings use multiple techniques, including next-generation Machine Learning algorithms to block the broadest possibilities & types of email threats. We combine email gateway with API-based scanning to protect inbound, internal, and external email, as well as cloud file sharing for O365/M365. Then, we provide DLP and advanced threat protection for OneDrive for Business, SharePoint Online, and Microsoft Teams.
Protect O365/M365 Emails
O365/M365 Data Lifecycle Management
As an organization, your client’s data is your stock in trade. You need to back it up continuously and protect it with complete predictability. For this, you need to ensure that every data-related disaster recovery effort is successful and that your customers can always access their data. To ensure this, you need to skillfully cruise through the data lifecycle management. We help you do that. From assessing how data is created, stored, used, accessed, and destroyed in your business to understanding how your business maintains compliance and continuity, we simply take up this responsibility and rejuvenate your O365/M365 data lifecycle.
Security Assessments that are accurate, dependable, and specific to your specific needs
Cyber Security Assessments
Cybersecurity failures can threaten your profitability, your integrity, and most importantly the brand You, not to mention the heavy penalties or fines from regulatory agencies in case of any failure. That’s why it’s important to know exactly where the weak spots are before someone else does! We do that accurately and reliably without requiring you to do in-house upskilling.
(GDPR) Compliance Assessment
General Data Protection Regulation (GDPR) Compliance Assessment is a high-impact service that examines your existing architecture, performs an in-depth analysis, and provides actionable recommendations for ongoing GDPR compliance, tailored to your specific business needs and growth targets.
Securing confidential business information from unauthorized access and exploitation requires leveraging a combination of the appropriate people, process, and technology. WME has everything in stock.
With today’s security risks it’s become harder for companies to stay on top of ever-increasing threats. WME is your premier partner when it comes to mitigating risk and being proactive with cybersecurity. We understand the difficulties in developing, implementing, and maintaining a vigilant security plan that fits your business.
Security Starts Within, We Do the Same
Why Choose us
for your Office 365 / Microsoft 365 Security and Compliance consultancy?
We assess your specific requirements
Different organizations have different security & compliance preferences depending upon their size, location, industry and many other factors. Our O365/M365 security consultants have experience working with a diverse range of companies. We cater to any security options you’re interested in including HIPAA or Sox, as well as two-factor authentication or any other relevant security measures.
We work at your ideal timeline
We care about your timeline. sometimes, you need work done immediately while at other times, you may prefer a slower pace to ensure no stone is left unturned. Our security & compliance experts are always flexible enough to with you at your preferred time and date. Make sure you are ready to initiate actions, we got you covered.
A win win work agreement
Once we have your specific requirements & growth plans outlined and timeline documented, we will come up with an agreement that makes sense for both stakeholders. This will be an exclusive, tailored-to-your-needs agreement offering all the flexibility you need to get going.
A speedy & predictable action
Finally, we start off. As per our reputation, we often exceed your requirements and timeline expectations. Then, we never disappoint you. We are always willing to analyze, recommend and implement your Office 365 / Microsoft 365 security & audit needs today.
From Small-to-mid businesses to Enterprises,
Here’s Why Businesses Choose WME
As experts in Microsoft IaaS and O365/M365 migrations, we can help design and support your deployment solution.
- Protect Active Directory with MS Defender for Identity
- Insider Risk Management
- Data Loss Prevention (Emails, SharePoint, OneDrive)
- Protect Office 365 Emails
- O365/M365 Data Lifecycle Management
- Protect ADFS with Defender for Identity